Corporate espionage is a very real threat
Levels of corporate espionage have significantly increased across all industry sectors in recent years, with the financial crisis exacerbating the problem. Technological advances and an increasingly transient workforce have contributed to the steady rise in espionage levels during the past decade. More recently, the increased competition between companies, heightened workplace pressures, large-scale redundancies and cost-cutting measures caused by the financial crisis have contributed to a dramatic proliferation in the scale and frequency of acts of espionage.
Read More
ASIS International recently held their 2010 international conference and exhibition in Dallas, Texas USA. I was lucky enough to have attended this exhibition and was absolutely amazed at just how many vendors were displaying state-of-the-art closed circuit television (CCTV) systems. Every step you took, was under surveillance. It is for this reason that I am shocked and amused to think that someone would be foolish enough to steal anything from such an exhibition, not to mention one of the world’s largest security exhibitions! Well, believe it or not, it happened!
Apparently, on the second morning of the ASIS 2010 Conference, several exhibitors reported that various items had been stolen from their exhibition stands. That’s right – a security exhibition is robbed! One of the victims was smart enough to approach a nearby exhibitor, who had several overt surveillance cameras pointing in the direction of the theft.
Read More
via Steven J. Vaughan-Nichols
The only thing “new” about Firesheep is that how it easy makes it to do. I’m unimpressed. Anyone who was serious about grabbing your personal information has already been doing it for years. Trust me, if someone really wanted your data and you’ve been using open Wi-Fi networks, they already grabbed it.

No, the real worry isn’t about some jerk grabbing your Twitter password in a coffee house.
The real worry has always been that your office Wi-Fi is easy to compromise and then someone can use a
packet-sniffer to get something that really matters like your your Accounts Payable password. (
more)
Need a Wi-Fi Security Audit and Compliance Inspection? (you do) Please call me. (more)
11/4/10 – UPDATE: IBM researchers are proposing an approach to WiFi security they call Secure Open Wireless in light of the release of the Firesheep tool. (more)
11/5/10 – UPDATE: 10 Ways to Protect Yourself from Firesheep Attacks (more)
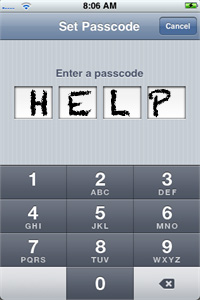
I give spy coins to my clients.It is a reminder that information loss is mostly a people problem, not an electronic problem. Filing cabinets of information can walk out the door in pocket change!
Careless people often blab information, forget to secure it, toss it in the garbage can, or otherwise lose it—hundreds of laptops are lost every day. People also steal it when they become greedy, spiteful, conned, blackmailed, or caught up in a “cause.”
Investigating an information loss, however, begins with an electronic surveillance detection audit.
Here’s why…
• Serious espionage will include electronic surveillance.
• The possibility must be resolved before accusing people.
• Bugging is the easiest spy technique to discover.
• Electronic surveillance evidence helps prove your case.
Best advice… Conduct audits on a regular basis. Uncover signs of espionage during the intelligence collection stage, before your information can be abused. (more)
A client reports back…
 “I think of all of the trinket type things we’ve accumulated over the years, the spy coin is *by far* the coolest, and is made even cooler with the background story provided on the chip!!
“I think of all of the trinket type things we’ve accumulated over the years, the spy coin is *by far* the coolest, and is made even cooler with the background story provided on the chip!!
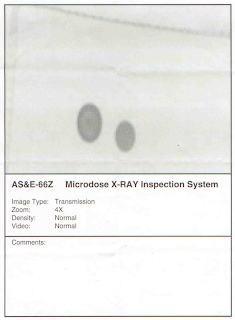
I took mine with me to the FBI building today and had the guards there X-ray it along-side of a normal quarter to see if its secret contents could be seen on an “airport quality” X ray machine. They printed out a copy of the scan image, I’ve attached it to this email for your amusement as well.
Several agents commented on how well it was made, and how hard it would be to detect such a thing.“